Category: Technical
-
DFS in a Windows Server Infrastructure & DFS Replication
DFS (Distributed File System) is a Windows Server feature which allows System Administrators to create a single namespace to provide a replicated sharing infrastructure across the network. Large enterprises that have multiple offices interconnected must be able to allow their employees to access documents easily. This means that clients must connect to desired resources from […]
-

What is HIPAA Compliance?
HIPAA stands for the Healthcare Insurance Portability and Accountability Act of 1996. This specifies laws for the protection and use of Personal (or Protected) Health Information (PHI) – essentially, your medical record. HIPAA sets the standard for protecting sensitive patient data. The Administrative Simplification provisions of the Act (HIPAA, Title II) require the U.S. Department […]
-

NAP Enforcement (Network Access Protection)
NAP or Network Access Protection is a Windows Server security mechanism which enables you to control how computers gain access to network resources. The main functionality of NAP is to verify and ensure that only healthy computers will be marked as compliant and will receive network access. In this article we will talk about some […]
-

CIFS Monitoring & Industrial PC Security
CIFS – How to Protect Legacy Industrial PCs (IPCs) Before the popularity of cloud began to take over, the only choice that companies large and small had with regard to IT infrastructure, was to build their own network. This of course consisted of servers, web servers and workstations, all connected together for the purposes of […]
-

Common Printing Issues in Windows 8 – Troubleshooting Tips
Windows 8 has undergone a lot of change when compared to its predecessor Windows 7. One of the most noticeable changes in the OS is the new interface with tiles, a.k.a the Metro UI, which works on touch screens, as well. With the modern interface, users might sometimes feel like they are using two operating […]
-

How to use Windows Firewall to Authorize Connections
In this article I will show you how to use Windows Firewall to authorize connections before data can be sent between devices. Authorization offers you an extra security layer and should be used whenever possible. There are services or applications that include authorization rules so that only allowed users/computers can connect to certain network resources. […]
-

The Best Windows Server Back-up Software
Historically, businesses have taken a somewhat lackadaisical approach to backing-up data. These days, while the cloud has allowed for an easier transition into data protection, sadly, many businesses still fail when it comes to backing up daily. In fact, a survey carried out this year found that a huge 53% of SMEs fail to carry […]
-

Is your Network Being Monitored by the NSA?
This year has proved to be something of an embarrassment for the US and UK governments, both having been caught red-handing spying on their own, and other country’s, citizens by whistle-blower Edward Snowden. Of course, it’s not the government themselves so to speak, but the agencies the US National Security Association (NSA) and UK Government […]
-
Configuring a Public Key Infrastructure-Pt. 2
Part 2, Continued from “How to Configure a Public Key Infrastructure on a Windows Server – Part 1” Enable the policy and check the Renew expired certificates, update pending certificates and remove revoked certificates and update certificates that use certificate templates check-boxes: Now we have to configure certificate templates for auto-enrollment. Open the Certification Authority […]
-
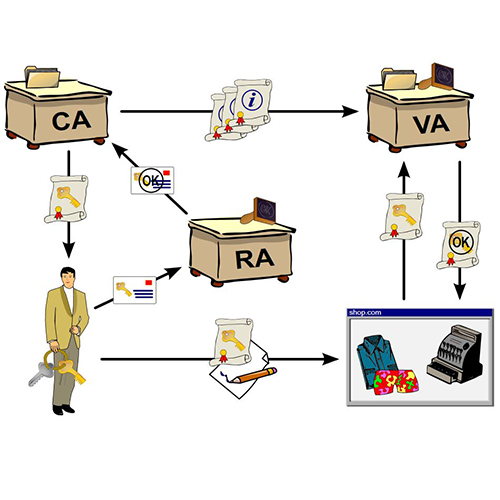
How to configure Public Key Infrastructures
In today’s article we will discuss implementing a PKI (Public Key Infrastructure) on a Windows Server 2008. The PKI will be used to authenticate wireless users. Note that the steps indicated here can also be applied to Windows Server 2012 versions. Before proceeding to the actual practice example, we’ll have to get acquainted with the […]